Pipeline Secret Groups
Infrastructure Provisioners require secrets to run the Terraform scripts and these secrets can be a line or multi-line string, which can exist in a file. They provide the authorization for the terraform scripts to create or make changes to the infrastructure.
A new first-class object called Pipeline Secret Groups requires two (2) inputs as given below:
- Name: Name of the secret group
- List of Secrets:
- File path: The file path used during the runtime
- Secret: The file content
Secrets can be any of the following:
- access_key/secret_key
- SSH keys
- Certificates
- Username/Password
Note: Pipeline Secret Groups can contain multiple secrets in it
Create Pipeline Secret Groups¶
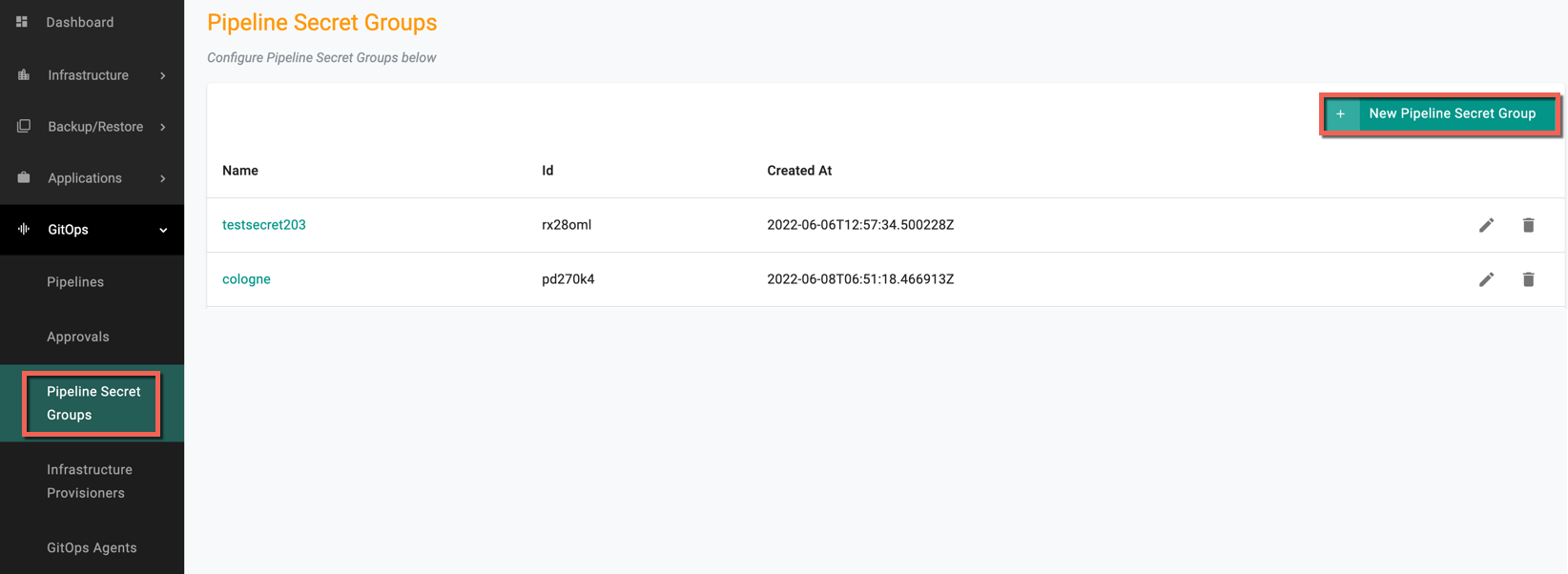
- In the controller, select Pipeline Secret Groups under GitOps and click New Pipeline Secret Groups
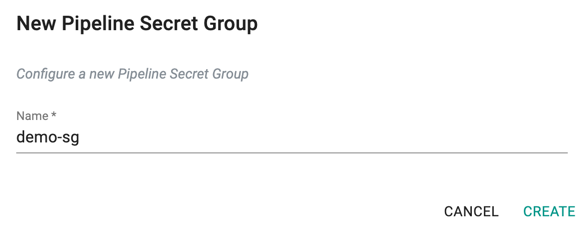
- Enter a name for the Secret Group and click Create
-
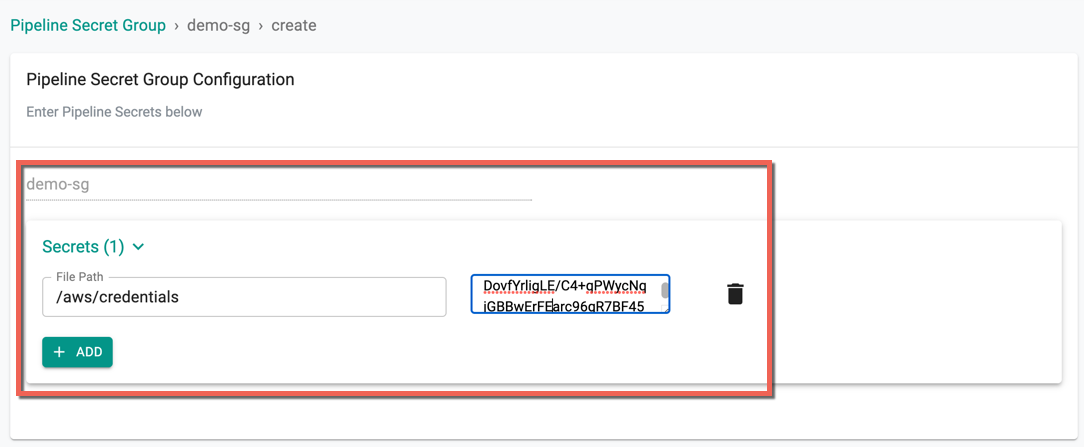
Click Add to add one or more secrets
-
Provide the file path mentioned in the terraform script
- Provide the secret
An illustrative example of Terraform Script is given below
terraform {
required_providers {
aws = {
source = "hashicorp/aws"
version = "~> 3.27"
}
}
required_version = ">= 0.14.9"
}
provider "aws" {
shared_credentials_file = "aws/credentials"
profile = "dev"
region = "us-west-2"
}
resource "aws_instance" "app_server" {
ami = "ami-0892d3c7ee96c0bf7"
instance_type = "t2.xlarge"
tags = {
Name = "MyDemoInstance"
}
}
- On successfully adding the required details, click Save
Infrastructure Provisioners or Pipelines can use this object in Terraform scripts