Releases - April 2023¶
28 Apr, 2023
v1.24¶
Amazon EKS¶
Spot Instances¶
Default selection for Spot Allocation Strategy has been changed with this release to 'capacity optimized' in line with recommended best practices.
Nodegroups¶
The default setting for a nodegroup in an EKS cluster will be set to be managed with this release in line with recommended best practices. This applies both when the cluster is provisioned and also when a new nodegroup is added through the user interface.
Google GKE¶
Cluster Templates¶
This allows platform teams to enable developer self-service for provisioning Google GKE clusters without losing control over governance and policy. Infrastructure admins can specify and encapsulate the freedom/restriction for infrastructure resource creation, abstracting the details of the resource creation by exposing limited configuration for the user to deal with.
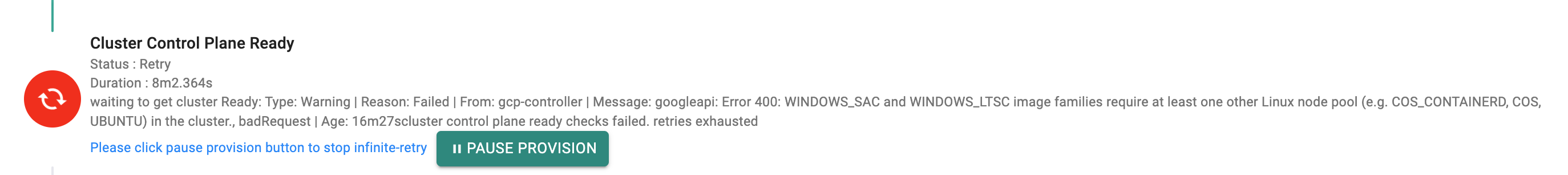
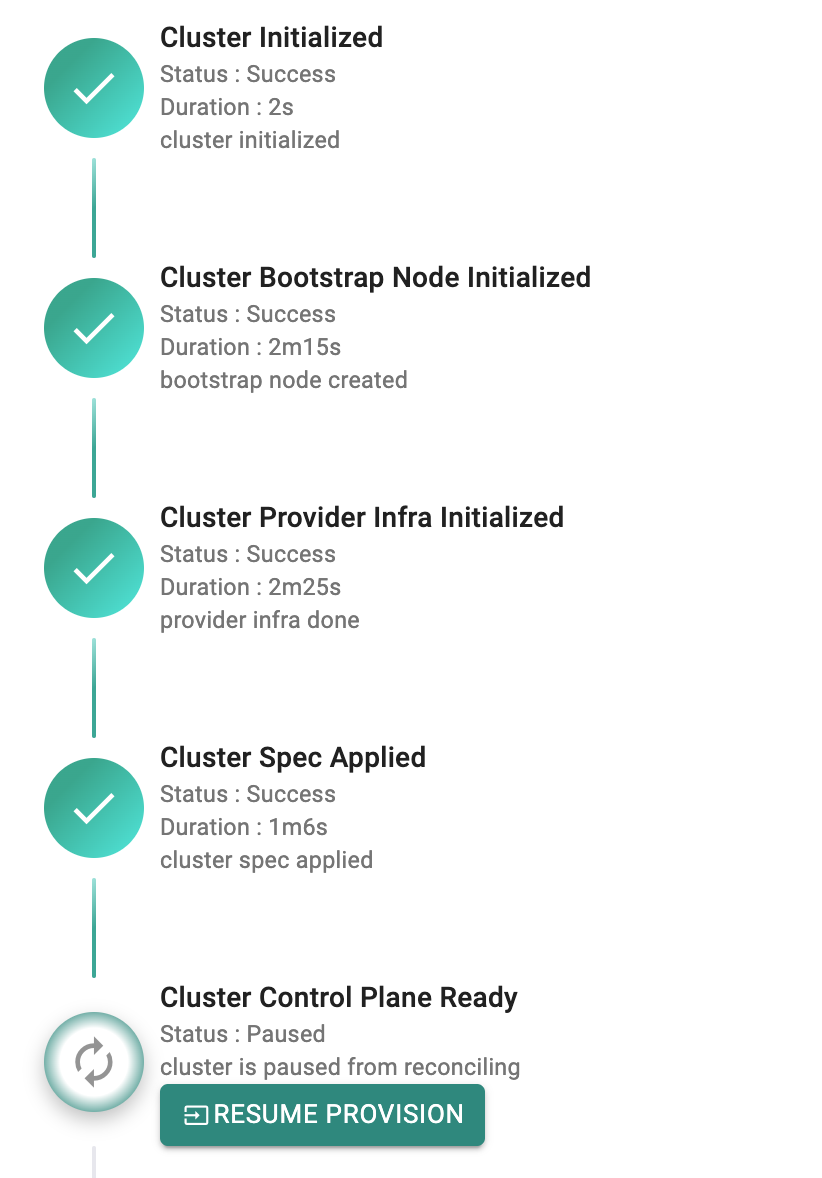
Pause/Resume for Cluster Provisioning¶
There are cases where cluster provisioning can be unsuccessful due to incorrect configuration(s) or other reasons. Instead of having to start from the scratch, it is now possible for customers to pause, remediate the issue and resume the cluster provisioning process.
Upstream Kubernetes¶
Support for Cilium CNI¶
Customers now have the option of selecting Cilium as the CNI provider with this release.
Clusters¶
Prevent accidental deletion of cluster resources¶
On a 'cluster delete' operation through the UI, the user is now asked for a confirmation to prevent accidental deletion of resources for clusters provisioned through the platform.
Cluster Blueprints¶
Blueprint Sync Performance¶
The cluster blueprint synchronization workflow has been tuned and optimized for better performance resulting in faster synchronization and convergence of cluster blueprints.
Managed Add-On Updates¶
Managed add-ons have been updated to later versions to ensure that vulnerability scans pass successfully.
Workloads¶
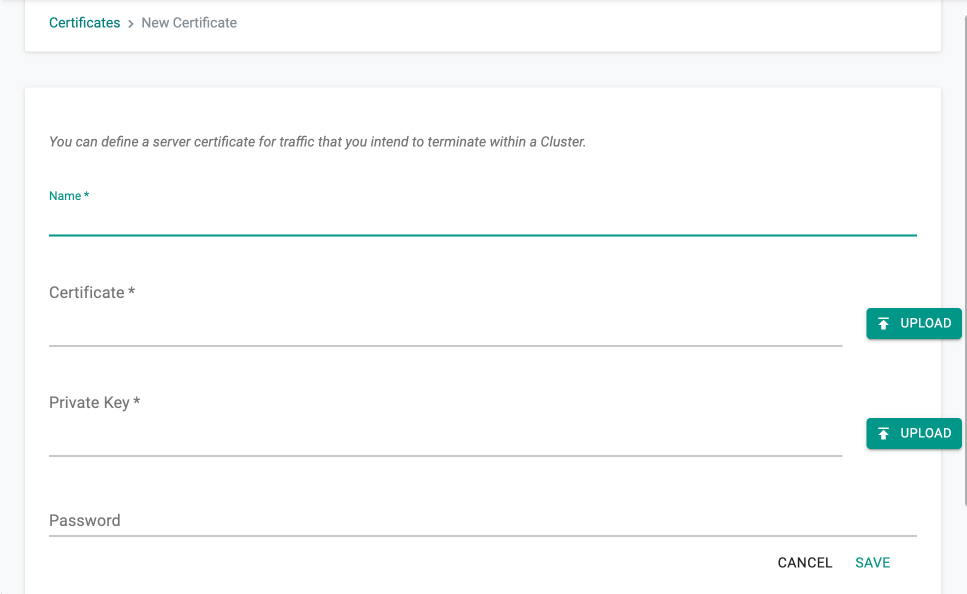
Certificates¶
It is now possible for customers to upload the certificate and the private key as a file. Supported file formats are .pem and .crt.
GitOps¶
Multi Arch for GitOps agent¶
The components deployed as part of the GitOps agent are now cross compiled. GitOps agent can now be deployed on both AMD64 and ARM64 architecture-based clusters.
SSO¶
Performance Optimizations¶
Single Sign On (SSO) operation for users with a very large number of groups from the Identity Provider (IdP) has been optimized for significant improvements in performance. With this, end users will see a dramatically faster login experience.
RBAC¶
Zero-Trust Access with multiple read/write roles¶
The organization's access policy is now enforced granularly for pod/exec operations for scenarios where the user has multiple read/write roles. With this, customers can configure and enforce extremely fine grained access policies for their developers.
Deprecation¶
Managed Log Aggregation Add-On¶
The managed log aggregation add-on (based on Fluentd) in the cluster blueprint has been removed with this release. Users are recommended to migrate to next generation alternatives such as Fluentbit based on the integrated catalog.
Workload Wizard¶
For Workloads of type Wizard, “Use system domain” is no longer available with this release as an option under Ingress configuration.
Bug Fixes¶
| Bug ID | Description |
|---|---|
| RC-19923 | UI: Reason for failure not displayed when chargeback report generation is unsuccessful |
| RC-24614 | Restore Job fails due to the name exceeding the limit for maximum allowed characters |
| RC-23155 | Self-managed Windows Node Group with custom AMI fails during an upgrade |
| RC-12119 | Issues with blueprint sync when same cluster names are used across different projects in an org |
| RC-22709 | UI: Issues with text wrapping for Blueprint event messages |
| RC-23448 | Cluster creation through RCTL fails when nodes are not specified in the spec file |
| RC-18693 | UI: Default value for max number of pods for AKS is set to 40 instead of 110 |
| RC-23583 | IDP user having org admin privileges is not able to delete an API only user using TF |
| RC-24334 | Pod failures due to Secret Store mutating Webhook policy set to Never |
| RC-24103 | Intermittent issues with deployment of v1-logging-infra during the blueprint sync process |
21 Apr, 2023
Self Hosted Controller v1.23 for EKS (with Custom Registry option)¶
The Self Hosted Controller software for EKS has been updated to support use of customer's own registry from where controller and cluster images can be pulled.