Managing Environments at Scale with Fleet Plans
As organizations scale their cloud infrastructure, managing dozens or even hundreds of environments becomes increasingly complex. Whether you are rolling out security patches, updating configuration variables, or deploying new template versions, performing these operations manually on each environment is time-consuming, error-prone, and simply unsustainable.
Fleet Plans solve this challenge—a powerful feature that eliminates the need to manage environments individually by enabling bulk operations across multiple environments in parallel.
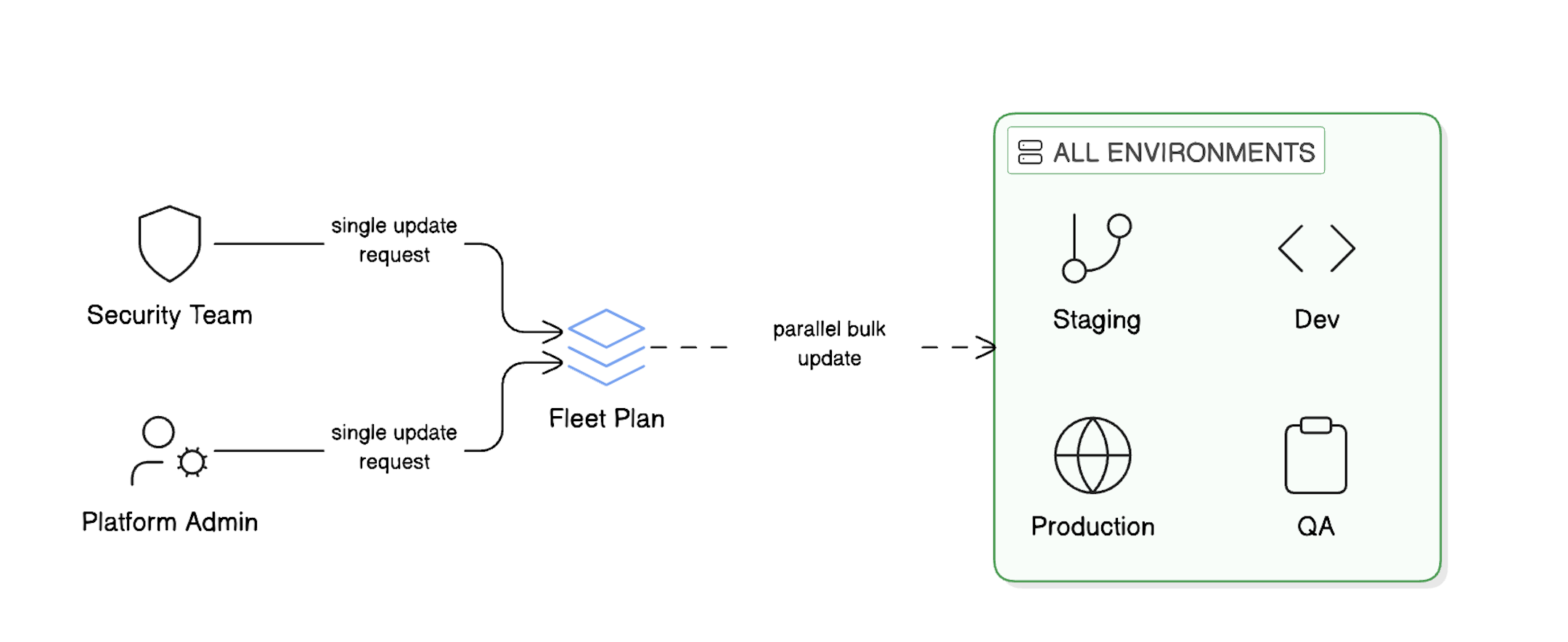
Fleet Plans provide a streamlined workflow for managing multiple environments at scale, enabling bulk operations with precision and control.
Note: Fleet Plans currently support day 2 operations only, focusing on managing and updating existing environments rather than initial provisioning.
