v4.1 Update 4 - SaaS¶
30 Apr, 2026
Bug Fixes¶
The following bug fix is included in the v4.1 Update 4 release:
| Bug ID | Description |
|---|---|
| RC-44798 | Fixed an issue where override values could not be saved for YAML-type configuration; saving overrides for Helm-type configuration was unaffected. |
v4.1 Update 3 - SaaS¶
Fleet Plan¶
GKE Support¶
Fleet Plans now support Google Kubernetes Engine as a cluster type. You can create a Fleet Plan with GKE clusters and perform bulk Day 2 operations such as blueprint updates, node pool changes, and Kubernetes version upgrades across multiple GKE clusters simultaneously. This extends the existing Fleet Plan support for Amazon EKS and Azure AKS clusters.
Benefit
Manage Day 2 operations across large fleets of GKE clusters from a single Fleet Plan, reducing operational overhead and ensuring consistent configuration at scale.
Fleet Plans are Cluster-Type Specific
Fleet Plans are currently scoped to a single cluster type. EKS, AKS, and GKE clusters cannot be combined into the same Fleet Plan — a separate Fleet Plan must be created for each cluster type. Support for cross-cluster-type Fleet Plans (for common operations such as blueprint updates) is planned for a future release.
For more information, see Fleet Plans.
Google GKE¶
Day 2 Operations¶
This release expands Day 2 operations support for Google Kubernetes Engine (GKE) clusters. The following cluster configuration options can now be updated post-provisioning:
| Configuration | Supported Operation |
|---|---|
| Cloud Logging | Enable/disable and update logging components |
| Cloud Monitoring | Enable/disable and update monitoring components |
| Managed Service for Prometheus | Enable/disable |
| Application Manager Beta Addon | Enable/disable |
| Backup for GKE Addon | Enable/disable |
| GCP Filestore CSI Driver Addon | Enable/disable |
| Image Streaming | Enable/disable |
disableHttpLoadBalancing |
true/false (default: false) |
disableHorizontalPodAutoscaling |
true/false (default: false) |
enableGcsFuseCsiDriver |
true/false |
| Legacy Authorization | Enable/disable |
| Google Groups for RBAC | Enable/disable and update security group |
| Workload Identity | Enable/disable |
Benefit
Update GKE cluster add-ons, networking, and security settings in-place without reprovisioning, giving platform teams greater flexibility to manage cluster configuration over time.
Azure AKS¶
Node Auto-Provisioning (NAP) with Proxy Support¶
AKS clusters configured with Node Auto-Provisioning (NAP) can now be provisioned with a proxy. A previously enforced validation block has been removed — this restriction existed due to an earlier Azure platform limitation that has since been resolved. You can now bring up AKS clusters with both NAP and proxy configured together without any additional workarounds.
Benefit
Unblocks AKS deployments in network-restricted environments that require a proxy, while still leveraging Node Auto-Provisioning for automated node management.
Bug Fixes¶
The following bug fix is included in the v4.1 Update 3 release:
| Bug ID | Description |
|---|---|
| RC-47085 | Fixed an issue where GitOps pipelines were not triggered after an out-of-band Kubernetes version upgrade sync on GKE clusters. |
v1.1.62 - Terraform Provider¶
An updated version of the Terraform provider is now available.
The following enhancement is included in this release:
| Resource | Enhancement |
|---|---|
rafay_gke_cluster |
Added Day 2 operations support for GKE cluster configuration, including cloud logging, cloud monitoring, add-ons, networking, and security settings. See the GKE Day 2 operations for reference. |
v4.1 Update 2 - SaaS¶
13 Apr, 2026
Integrations¶
Repositories¶
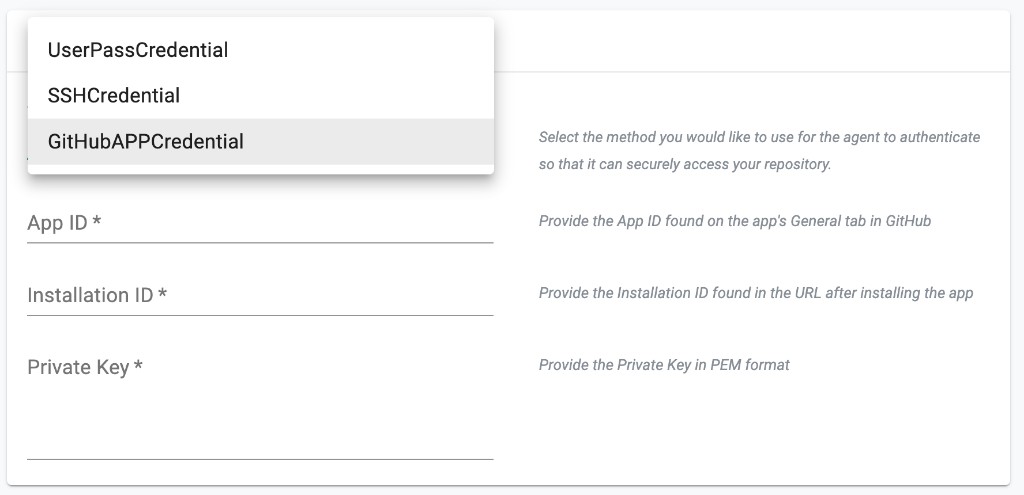
GitHub App Credentials¶
Repositories now support GitHub App Credentials (GitHubAPPCredential) as an authentication method. This allows you to authenticate to GitHub using a GitHub App instead of a personal access token or SSH key.GitHub App Credentials are supported across all interfaces — UI, Terraform, API, and CLI (RCTL).
The following fields are required:
| Field | Description |
|---|---|
| App ID | The GitHub App ID, found on the app's General tab in GitHub. |
| Installation ID | The installation ID, found in the URL after installing the app. |
| Private Key | The private key associated with the GitHub App, in PEM format. |
Benefit
Authenticate to GitHub repositories using a GitHub App for improved security and fine-grained access control, without relying on personal access tokens or SSH keys.
For more information, see GitHub App Credential and the Terraform provider documentation.
Bug Fixes¶
The following bug fixes are included in the v4.1 Update 2 release:
| Bug ID | Description |
|---|---|
| RC-48317 | Fixed an issue where values.yaml files were not being updated through pipelines for workload templates. |
| RC-48526 | Fixed an issue where Helm override was referencing the existing value file instead of the newly updated one. |
v1.1.61 - Terraform Provider¶
An updated version of the Terraform provider is now available.
The following enhancement is included in this release:
| Resource | Enhancement |
|---|---|
rafay_repositories |
Added support for the new GitHubAPPCredential credentials type for repository integration. See the GitHub App credentials example for reference. |
v4.1 Update 1 - SaaS¶
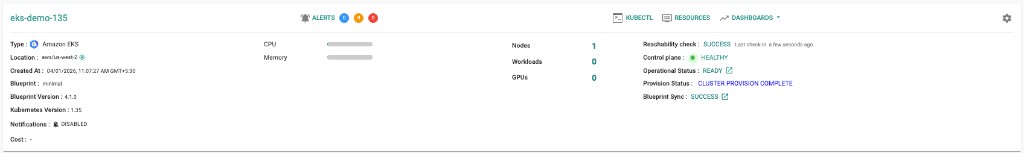
Amazon EKS¶
Kubernetes v1.35¶
New EKS clusters can now be provisioned based on Kubernetes v1.35. Existing clusters can also be upgraded in-place to Kubernetes v1.35.
Azure AKS¶
BYOCNI with Cilium Support¶
This release adds support for BYOCNI (Bring Your Own CNI) with Cilium on AKS clusters. To enable this, set networkPlugin to none in the AKS cluster configuration and apply a blueprint that includes the Cilium add-on. Ensure the pod CIDR is consistent between the network configuration and the Cilium add-on values so that the cluster initializes successfully.
Benefit
Ensures consistent Cilium networking across clusters, with the flexibility to customize the configuration through the blueprint workflow.
For more information, see BYOCNI with Cilium.¶
Bug Fixes¶
The following bug fixes are included in the v4.1 Update 1 release:
| Bug ID | Description |
|---|---|
| RC-47916 | MKS: Fix Kubernetes version upgrade from 1.30 to 1.31 |